Discover why Zero-Trust Architecture is the cornerstone of cybersecurity in 2026. Learn how to secure your remote workforce with identity-centric security, micro-segmentation, and AI-driven threat detection.
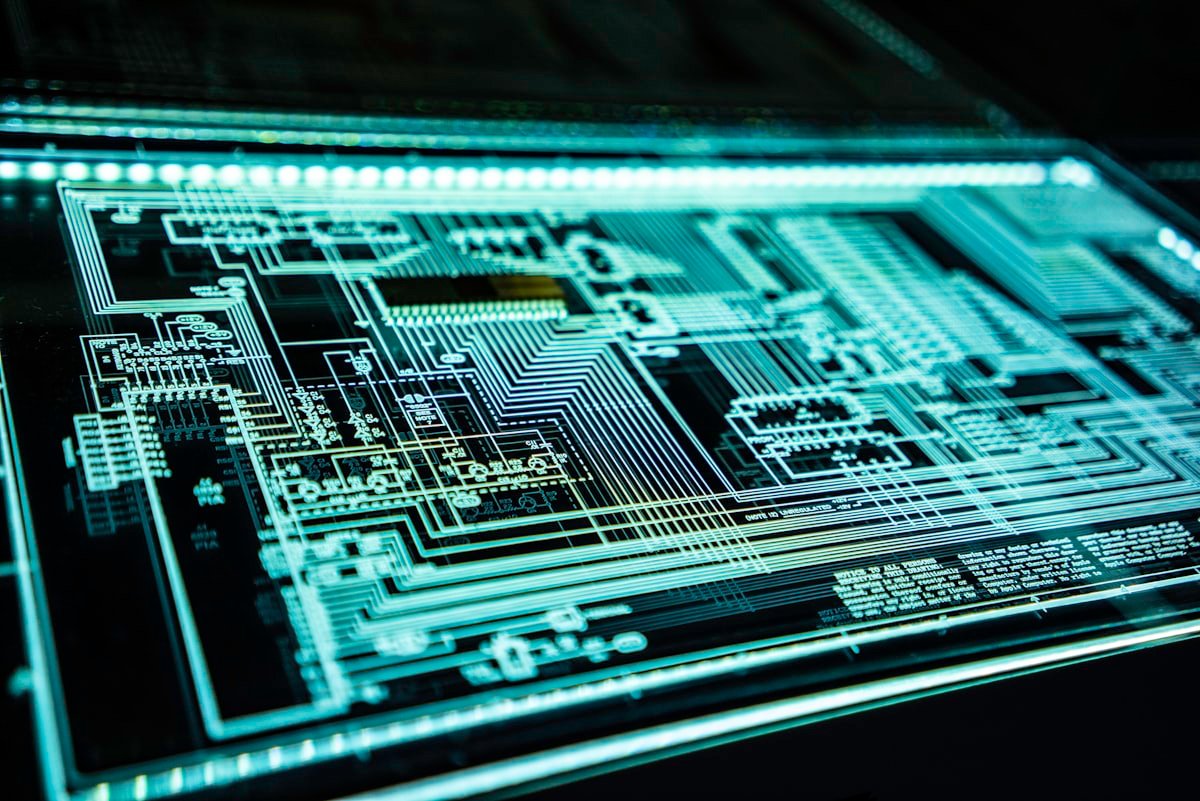
<h1>The Future of Zero-Trust Architecture: Securing Remote Workforces in 2026</h1><p>In the rapidly evolving digital landscape of 2026, the traditional perimeter-based security model has become obsolete. With the permanent shift toward hybrid and fully remote work environments, organizations can no longer rely on ‘moat-and-castle’ defenses. Enter <strong>Zero-Trust Architecture (ZTA)</strong>—a strategic approach to cybersecurity that eliminates implicit trust and continuously validates every stage of digital interaction.</p><h3>The Shift from Perimeter to Identity</h3><p>The fundamental principle of Zero Trust is simple: \"Never trust, always verify.\" In 2026, identity has become the new perimeter. Whether an access request originates from inside or outside the corporate network, the system must verify the user's identity, the device's health, and the context of the request before granting access to specific resources.</p><h3>Micro-Segmentation: Reducing the Blast Radius</h3><p>One of the critical components of Zero Trust is micro-segmentation. By breaking the network into small, isolated zones, organizations can prevent lateral movement by attackers. If a single device is compromised, the threat is contained within that specific segment, significantly reducing the potential ‘blast radius’ of a security breach.</p><h3>AI-Driven Threat Detection and Response</h3><p>In 2026, the volume and sophistication of cyber threats are beyond human capacity to manage manually. AI-driven security operations centers (SOCs) now play a pivotal role in Zero-Trust frameworks. These systems analyze vast amounts of telemetry data in real-time to identify anomalies and respond to threats at machine speed.</p><h3>Conclusion</h3><p>As we move further into 2026, Zero-Trust Architecture is no longer an optional strategy—it is a necessity for any organization operating in a digital-first world.</p><h2>FAQs</h2><p><strong>1. What is Zero-Trust Architecture?</strong><br>Zero-Trust Architecture is a cybersecurity framework that requires all users to be authenticated, authorized, and continuously validated.</p><p><strong>2. Why is Zero Trust important for remote work?</strong><br>It ensures that users accessing the network from unsecured home environments are strictly verified, protecting corporate assets from potential breaches.</p><p><strong>3. What is micro-segmentation?</strong><br>It is the process of dividing a network into smaller segments to limit the spread of an attack.</p><p><strong>4. How does AI help in Zero Trust?</strong><br>AI detects real-time anomalies and automates responses to security threats that human operators might miss.</p><p><strong>5. Is Zero Trust expensive to implement?</strong><br>While it requires initial investment, it significantly reduces the cost associated with major data breaches and improves overall compliance.</p>